How Websites Are Hacked in 2024 and Useful Tips on How to Prevent It
Understanding how websites get hacked is crucial for anyone who manages or uses online platforms. This article aims to clearly explain the main methods hackers use to compromise websites and provide practical advice on how to prevent such security breaches.
By familiarizing yourself with these common vulnerabilities and implementing the safeguards discussed, you can significantly reduce the risk of your website falling victim to an attack.

Why Are Websites Hacked
Hackers are driven by various motivations, each carrying its own threats to website owners.
Value of Data
Private data such as financial records, login credentials, and other sensitive information collected on web servers are highly sought after by cybercriminals.
Confidential information, when stolen, can be trafficked on the dark web, employed in identity theft, or used for blackmail purposes.
A website’s size does not diminish the value of its confidential data. Any site that stores private information can attract a hacker’s interest.
Financial Gain
Financial gain is another strong motivator for hackers. They may deploy ransomware to lock website owners out and extort money to restore their access.
Another less flashy approach is to discretely break into your system to siphon funds by intercepting financial transactions between your business and customers.
Political and Ideological Reasons
Some hackers are driven by a desire to make a statement by disrupting governmental or corporate operations.
These cybercriminals, often referred to as hacktivists, may not always seek personal gain but can cause substantial damage and loss of public trust in targeted organizations.
How Websites Are Hacked
Let’s look at some of the most common hacking techniques attackers use to access a website.
Malware and Backdoors
Malware is a type of malicious software that infiltrates websites and computer systems, often exploiting security weaknesses such as outdated software, insecure coding practices, or third-party integrations. Once infected, they can cause frequent website crashes and security breaches.
A backdoor is an access control software vulnerability that can allow attackers to gain unauthorized access to your website. These can be flaws in the code or malware infections, allowing attackers to mislead login procedures to hijack the site.
Regularly scanning your site for malware is an essential security practice. Scans should be thorough and frequent, using reliable and updated security tools to identify the latest threats.
Here are a few well-regarded malware detection tools:
- Sucuri SiteCheck. A free website scanner that can detect various types of malware and security issues. They also offer paid features like website backdoor removal and firewall protection.
- Wordfence Security. A popular security plugin for WordPress websites that includes an endpoint firewall and malware scanner.
- SiteGuarding. A website antivirus and anti-malware software that scans for known malware, website errors, out-of-date software, and other vulnerabilities.
SQL Injection
An SQL injection (SQLi) is a type of cyber-attack where a hacker slips malicious code into a website’s database to alter or steal confidential data.
The attacker usually manipulates text input fields, like those used for login or search functions, to send SQL commands to the database to trick it into performing an unauthorized action, like providing direct access to the system.
For example, instead of entering a username, hackers might enter a short SQL code such as ‘ or 1=1 — to override the conditions set on user access points to validate someone as an authenticated user.
SQL injection prevention relies on thorough verification and sanitization of all user inputs, ensuring that only legitimate data is processed. This is known as input validation.
Moreover, using parameterized queries – where SQL code is defined and user input is treated strictly as data, not executable code – can effectively neutralize SQL injections.
Social Engineering
Social engineering is a type of psychological manipulation where attackers exploit vulnerabilities in human behavior to convince them to install malicious software on their personal computers, upload malicious files to their internal network, divulge login credentials, or even provide direct access to restricted areas.
Here are some common social engineering attacks cybercriminals use:
- Pretexting – attackers assume a false identity, often posing as trusted individuals like technical support staff or authority figures, to gain the victim’s trust and extract personal information or breach restricted systems.
- Baiting – hackers leave enticing lures, such as USB drives in public places or malicious links on social media forums, persuading curious individuals to interact with them.
- Quid pro quo – social engineers offer users something of value, such as a gift or a service, in exchange for personal information or entry into a restricted area.
- Phishing – hackers craft deceptive emails that direct users to malicious websites that appear to be from legitimate sources, such as banks or credit card companies, tricking unsuspecting individuals into revealing their login credentials or other sensitive data.
Cross-Site Scripting (XSS)
Cross-site scripting is a security vulnerability that allows attackers to inject malicious scripts into web pages. It allows cybercriminals to steal user data, deface websites, or redirect visitors to harmful sites.
XSS attacks can occur in various forms, often exploiting vulnerabilities in user-generated content.
Common examples include:
- Reflected XSS – malicious scripts are reflected back to the user’s web browser through URLs, error messages, or other dynamic content.
- Stored XSS – scripts are injected into a website’s database and executed whenever the affected page is loaded.
- DOM-based XSS – attackers inject scripts directly into a web page’s Document Object Model (DOM), exploiting vulnerabilities in JavaScript libraries or frameworks.
To effectively protect against XSS attacks, website developers and administrators must implement comprehensive security measures.
Key strategies include:
- Input sanitization – properly validate and sanitize all user-supplied data before it is displayed or processed. This involves removing or escaping any potentially harmful characters or code that could be injected into the web page.
- Content security policies (CSPs) – implement CSPs to define which sources can execute scripts on your website. This helps to restrict malicious scripts from being injected and executed.
- Regular security audits – conduct regular security audits of your website’s code to identify and remediate potential XSS vulnerabilities.
Brute Force Attacks
Brute force attacks are a trial-and-error method hackers use to decode encrypted data such as passwords. This is done by systematically checking all possible password combinations until the correct one is found. Attackers employ automated tools to generate password combinations.
The use of strong and unique passwords ensures effective brute force protection. Avoid using easy-to-guess passwords such as birthdays, names, or common words.
Another defense measure is to implement account lockout policies, which freeze user accounts after a certain number of incorrect attempts.
How to Prevent Website Hacking
Let’s delve into actionable hacking prevention strategies you can implement to safeguard your website.
1. Choose a Secure Hosting Provider
Choosing a secure hosting provider is your first defense against website hacking. A robust web host stores and secures your website data from numerous online threats.
Secure Web Hosting with Hostinger
When it comes to secure web hosting, Hostinger stands out as a premier choice. Apart from delivering a 99.9% uptime and maximum speed, our plans follow web hosting security best practices to provide a safe web development experience.
Key Security Features Offered by Hostinger
- Advanced DDoS protection – our hosting infrastructure is secured with cutting-edge DDoS protection mechanisms to shield your website against the disruptions caused by DDoS attacks.
- Continuous monitoring – the Hostinger security team constantly monitors our systems for unusual behavior, identifying and addressing potential security issues.
- Secure email hosting – our business email hosting service incorporates spam filters and malware scanning tools to protect customers from phishing attempts.
- Automated backups – all our web hosting plans incorporate automated website backup solutions to reduce the potential impact of data breaches or accidental data loss.
- Free SSL certificates – Hostinger plans provide unlimited free SSL certificates at no additional cost, ensuring that communication between your website and visitors is encrypted and secure.
- Web Application Firewall (WFA) – our plans come with a sophisticated web application security firewall that filters HTTP traffic for third-party access. It offers data breach prevention by protecting your website from a variety of application-layer attacks, such as SQL injections and cross-site scripting.
- Two-Factor Authentication – with Hostinger, you can enable two-factor authentication for your account, adding an extra level of security that neutralizes attacks such as phishing and brute force.
- ModSecurity integration – ModSecurity, an open-source intrusion detection and prevention system, is integrated into Hostinger’s servers to filter incoming traffic and block SQL injection attacks.
2. Use Strong and Unique Passwords
A strong, unique password combination is the first line of defense against breaches.
Here are some quick tips for creating and maintaining a strong password:
- Strength in complexity – mix uppercase and lowercase letters, numbers, and symbols to create a difficult-to-guess string of characters.
- Uniqueness matters – use different password combinations for each account to prevent one unfortunate breach from affecting other accounts.
We also recommend using password management tools to generate and securely store complex passwords.
Here are some trustworthy password managers you can rely on:
- LastPass – has a user-friendly interface and a wide range of features, including secure password sharing and emergency entry. Offers free and premium plans.
- 1Password – implements strong security measures and intuitive design. 1Password also includes a security audit feature to help you identify and fix weak passwords.
- Dashlane – provides a simple and secure way to manage your passwords and personal information. Purchasing a premium plan also includes a VPN, further boosting your online privacy and security.
Regular password updates are fundamental to avoiding security vulnerabilities. Periodically changing passwords disrupts an attacker’s ability to guess or crack your passwords through a brute force attack.
3. Learn to Identify Social Engineering Attacks
Social engineering attacks exploit human psychology rather than software vulnerabilities, yet awareness and vigilance are the most effective defenses against them.
Here are some social engineering awareness tips:
- Verify contact information – carefully check the sender’s email and website for inconsistencies or spelling errors, and hover over links to see their actual destination before clicking.
- Avoid unknown links and devices – steer clear of plugging unknown USBs, clicking on unfamiliar links, and opening attachments from sources you don’t recognize.
- Use two-factor authentication – 2FAs add a second verification step to your account, so even if someone gets your login credentials, they still won’t gain access to your account.
- Keep updated – cybercriminals constantly develop new ways to perform malicious attacks, and being aware can help you spot and avoid them.
- Install security software – use trustworthy security software for real-time protection against phishing attacks. Some of these tools also provide alerts for suspicious websites.
4. Perform Regular Software Updates
Regular software updates play a crucial role in securing websites, often including patches for security vulnerabilities discovered since the last version was released.
It is essential to ensure that all components of their website, including the content management system (CMS), plugins, and themes, are always up to date.
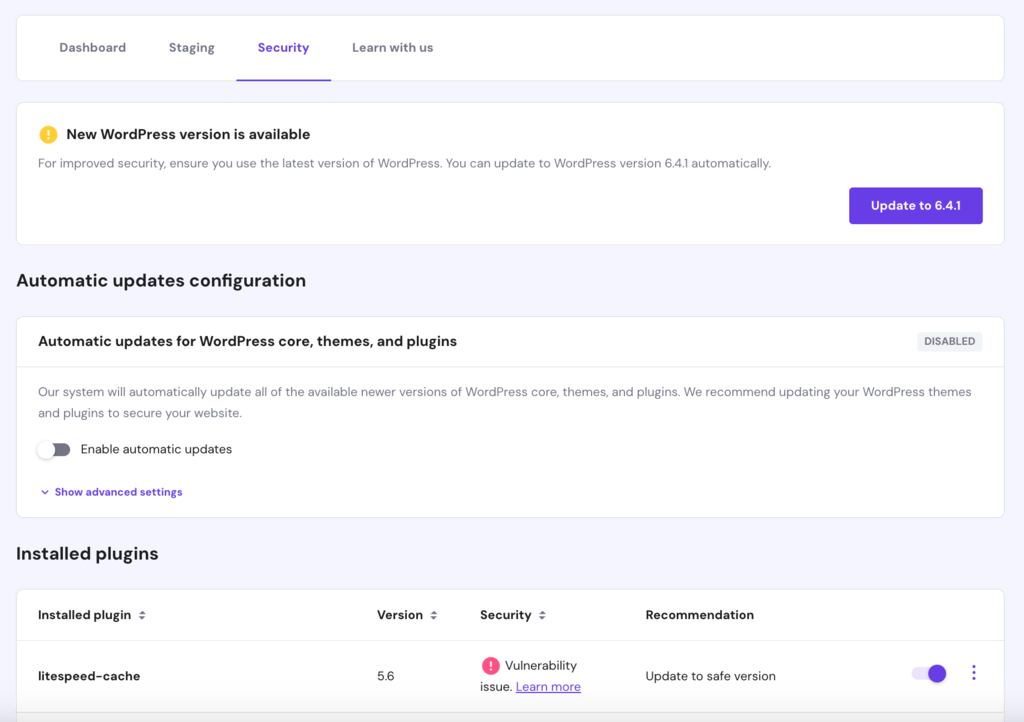
Hostinger’s hPanel simplifies this process by providing a streamlined interface where website owners can easily monitor and implement software updates and mitigate discovered vulnerabilities.
Pro Tip
Get a better site management experience with Hostinger hPanel. Learn more by reading our hPanel tutorial.
5. Setup Website Firewall and Security Plugins
Firewalls and security plugins are a website’s first defense against various security threats.
They monitor and filter incoming traffic, block malicious requests, and provide a protective barrier that makes it difficult for attackers to hack websites.
For WordPress websites, popular security plugins like Wordfence and Sucuri Security can significantly enhance a website’s security. These security toolkits offer features like real-time threat detection, continuous scanning for malware, and the ability to enforce strong password policies.
They also typically include a website firewall that can help prevent breaches.
6. Use SSL/TLS Encryption
SSL/TLS encryption is a critical security measure websites use to securely transfer data between the user’s browser and the web server software. This is especially important for websites that handle sensitive data, such as personal information, user credentials, or credit card numbers.
It can also improve a website’s visibility and credibility as search engines such as Google favor encrypted connections, often ranking secure sites higher.
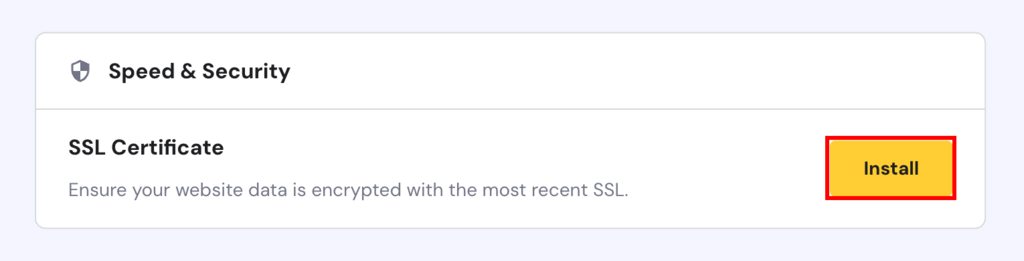
Fortunately, our hPanel offers a one-click setup that makes installing your free SSL certificates easier and hassle-free.
7. Perform Regular Backups
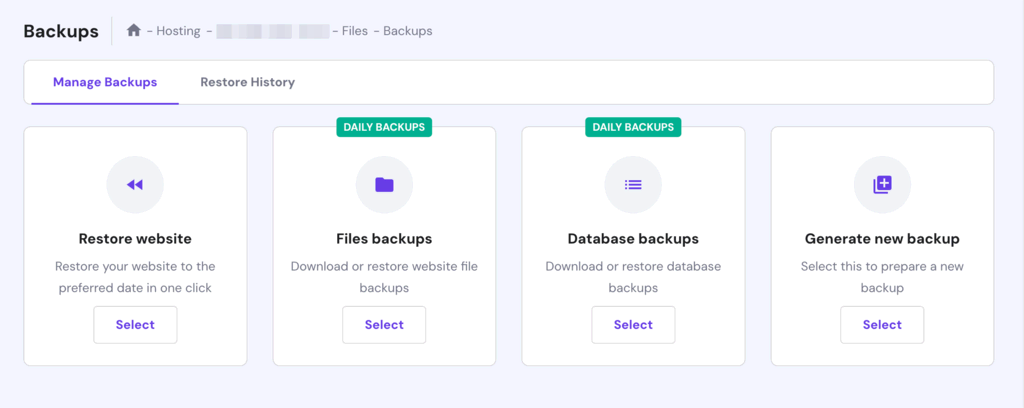
Regular backups are an essential part of maintaining your website’s security. They act as a safety net, allowing you to restore your website to a previous state in case of data loss, hacking, or accidental deletions.
Your hosting provider’s control panel typically allows for an easy configuration of automated backups.
Hostinger offers easy-to-configure automated backups that can occur daily, weekly, or custom intervals, ensuring your data is regularly captured without manual intervention.
8. Configure User Access Control and Permissions
Controlling who can access your website’s backend is crucial for maintaining security. By restricting user permissions, you can limit the likelihood of unauthorized changes, which could open security vulnerabilities or lead to data breaches.
Here’s how to manage user roles and permissions effectively:
- Assess user roles. Review the roles of individuals who need access to your website to determine the access level required to perform their duties.
- Assign permissions. Once those roles are defined, assign user privileges accordingly. For instance, a content editor might need access to the CMS but not the server controls.
- Regular reviews. Periodically review user roles and permissions, especially after role changes. It lets you identify suspicious admin accounts, which are indicators of a hacked WordPress site.
Hostinger simplifies access management thanks to Secure Access Manager (SAM), letting you assign precise access levels for team members. SAM safeguards your site from internal threats and simplifies role management tasks.
9. Stay Informed on Website Security Threats
Staying informed about the latest security threats can significantly elevate a website owner’s ability to tackle cyber attacks.
For robust security vigilance, remember to:
- Make a habit of checking prominent security blogs for the latest in vulnerabilities and defense mechanisms.
- Subscribe to reputable newsletters for tips on cybersecurity best practices and latest security developments.
- Engage with security forums such as Reddit’s cybersecurity threads or StackExchange for on-the-spot guidance and expert insight.
- Attend webinars and workshops from cybersecurity professionals for knowledge on prevailing threats and trends.
- Set up notifications through different services like Google Alerts or specialized cybersecurity alert platforms to stay informed about potential threats to your website.
Suggested Reading
Maintain your website using
Conclusion
Website security is an essential aspect of managing your digital presence. Hackers employ a range of techniques to exploit website vulnerabilities, from malware insertion to brute force attacks.
Understanding these methods is your first step towards identifying and mitigating online security risks to protect your website.
Here’s a quick recap of some of the most essential and actionable steps website owners can take to protect their sites:
- Choose a secure web hosting provider to ensure robust baseline protection.
- Regularly update software and plugins to close security gaps.
- Use strong passwords and change them periodically to prevent breaches.
- Install an SSL certificate to encrypt data and boost website user trust.
- Perform consistent backups to ensure you can restore your website if something goes wrong.
It’s important to remember that security is not a one-time setup but a continuous process.
Despite all this, it does not guarantee absolute invulnerability, but it can significantly reduce the risks and prepare you to respond effectively to security incidents.
Stay proactive, stay secure!
How Websites Are Hacked FAQ
Let’s address some frequently asked questions about website hacking.
What Websites Are the Most Commonly Hacked?
Websites with outdated systems, weak passwords, and inadequate security measures are often targeted. Hackers prefer sites with valuable data like personal and financial information but also attack websites to use them as tools for further attacks.
How Do I Know if My Website Has Been Hacked?
Signs of a hacked website include unexpected changes in content or design, new unknown accounts with admin privileges, sudden traffic drops, or security tool alerts. Unauthorized redirects and suspicious pop-ups are also common indicators.
What Happens When a Website Gets Hacked?
When a website is hacked, it may be used to distribute malware, launch other attacks, or steal sensitive data. The site’s reputation can suffer, causing search engines to blocklist it, leading to significant financial and data losses for both the owner and the users.