What Is a Hypervisor: Understanding How It Works, Main Features and Use Cases
A hypervisor is software for creating virtual machines, allowing you to run multiple operating systems on one physical server. It helps improve resource optimization, data security, infrastructure uptime, and scalability.
Depending on the type, hypervisors run on top of physical hardware or as a software layer application. In a virtual private server (VPS) environment, it is used to build, isolate, and allocate resources between virtual instances.
To help you understand this technology, this tutorial will explore all about hypervisors, including how it works and its benefits. We will also explain its types, features, use cases, and how to choose the right one for your needs.
What Is a Hypervisor?
A hypervisor is software responsible for creating isolated virtual machines in a server. It lets you run multiple operating systems on a single host machine, each with dedicated resource allocation.
The main function of a hypervisor is to create a multi-tenant hosting environment to optimize resources and costs. Moreover, it acts as a disaster recovery system, ensuring data safety.
How Do Hypervisors Work?
A hypervisor or a virtual machine monitor (VMM) creates an abstracting layer between physical hardware and software. It pools computing resources from the host, including the CPU, RAM, and storage.
A virtual machine accesses the hardware resources by sending the host machine a request, which the abstracting layer will translate. To facilitate communication and data transfer, the hypervisor uses various methods, including an API call.
It assigns each virtual machine a guest operating system (OS), CPU, RAM, and network allocation based on the request. Since the hypervisor allocates resources dynamically, it can redistribute hardware to different instances based on the requirements.
Independent resource allocation also creates an isolation layer between instances. It allows users to install their own operating system and software without affecting other virtual servers.
For example, users can install different operating systems from the host, like FreeBSD with a Windows Server. Moreover, isolation helps improve security since running risky Linux commands on a VM won’t affect others.
In addition, security flaws and cyber attacks on a virtual machine won’t impact the others. If one operating system fails, others will keep running without interruption.
Why Use a Hypervisor?
A hypervisor lets you create a cost-effective IT infrastructure. Instead of running several physical servers, web hosts can deploy one machine containing multiple virtual instances for many users or applications.
Running multiple physical servers may waste computing resources as you can’t repurpose them. Hypervisors let web hosts seamlessly reallocate unused hardware for another instance to optimize usage and improve system performance.
Other benefits of hypervisors include simplifying hosting infrastructure scaling for a higher workload. For example, you can quickly provision an additional virtual instance to run a new task with dedicated virtual resource allocation.
You can also easily move virtual machines to another host with the same hypervisors without incompatibility issues. It enables you to switch to a higher-performance machine without extensively reconfiguring the virtual environment.
Types of Hypervisors
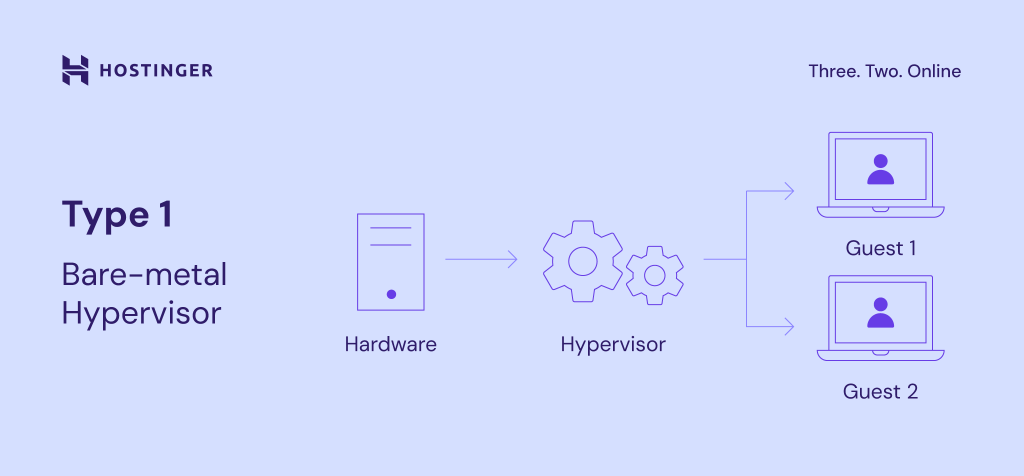
Depending on the abstraction layer position, there are two hypervisor types – type 1 and type 2 hypervisors. Both have the same purposes but differ in use cases and benefits.
Type 1 Bare-Metal Hypervisor
Type 1 bare-metal hypervisors run on physical hardware to create and manage guest operating systems. It schedules the virtual machines’ resource allocation directly to the host, reducing latency and improving performance.
Bare-metal hypervisors act as a lightweight operating system that can dynamically allocate resources to maximize the host hardware capacity. Since these virtualization technologies assign computing power dynamically, each virtual machine will only hit the limit when the workload meets the hardware’s resource constraints.
Moreover, users can easily migrate type 1 hypervisors to another host since they don’t depend on the host operating system. It also improves security as flaws in the software may increase virtual machines’ attack surface.
Due to its higher performance, type 1 hypervisor is commonly used in an enterprise data center and service provider infrastructure, like a web host. As such, it is generally unsuitable for new users due to the complicated setup process.
Popular examples of this type of hypervisor include Microsoft Hyper-V and VMware vSphere. Meanwhile, free options include the open-source Kernel-based Virtual Machine (KVM) and Oracle VM.
Important! Although KVM runs on the Linux kernel, it is considered a type 1 hypervisor for its ability to access the underlying hardware directly.
Type 2 Hosted Hypervisor
The type 2 hosted hypervisor runs on a conventional operating system. Since it doesn’t schedule the VM resource allocations directly against the underlying hardware, the process is slower and less efficient.
Resource optimization and management are also less flexible since some type 2 hypervisors can’t dynamically allocate computing hardware. For example, a virtual machine will always consume 8 GB of RAM if you assign the amount.
This hypervisor architecture is also less secure than the bare-metal one due to a lower isolation level. In addition, a security vulnerability in the host operating system may also compromise the virtual instances.
Despite its drawbacks, hosted hypervisors are simpler to set up and manage. You can install the virtualization technology as a software application on a personal system, just like other computer programs.
This type of hypervisor is ideal for running virtual machines with different operating systems for testing or development. Popular examples include Oracle’s VirtualBox, VMware Fusion, and Windows Virtual PC.
Key Features of Hypervisors
Hypervisors have several crucial features for creating a virtual server hosting infrastructure. Some of the most important ones are:
- Virtual Machine (VM) creation. Hypervisors allow users to create multiple isolated virtual instances on a single physical machine. In addition to optimizing costs, server virtualization helps improve workload distributions.
- Resource allocation. Users can use hypervisors to allocate server resources dynamically between virtual instances. It allows other environments to use the computing power surpluses for a more stable performance.
- Snapshotting. A hypervisor can capture the virtual machine’s system state and configurations at a specific time. This restore point lets users easily recover their data after accidents or when cloning server instances.
- Live migration. Users can move a virtual instance to another physical host without disrupting running processes or causing downtime. In addition to simplifying data migration, this feature acts as a failover system by switching the failed system to a healthy server.
- Resource monitoring and management. System administrators can allocate and reallocate the hardware resource pool to different instances. Moreover, they can easily monitor multiple instances’ resource consumption in one place using the hypervisor software.
Hostinger uses a type 1 bare-metal hypervisor to run virtual machines. By leveraging these features, we provide reliable and high-performance VPS hosting services.
Isolations ensure users can configure their hosting environment freely and improve data confidentiality. For example, they can install different operating systems and software according to the hosted applications’ requirements.
Moreover, we provide each virtual environment with a dedicated IP address to enable full root access, providing users with high customizability. Hypervisors’ snapshot and failover systems also help us improve our VPS security and uptime.
Suggested Reading
Check out our article on optimizing WordPress with KVM to learn more about hypervisor vs container performance for hosting.
Hypervisor Use Cases
In this section, we will explain several common use cases for hypervisors and their benefits.
Server Consolidation
Consolidation aims to minimize the number of physical machines to create an infrastructure and optimize resource usage. Users can do so by leveraging hypervisors’ server virtualization capabilities to create multiple virtual instances with dynamic hardware allocations.
In addition to saving costs, consolidation reduces power consumption and speeds up the system provisioning process. Moreover, it provides a single point of administration using the hypervisor management software like Red Hat’s virtual machine manager.
Consolidation also lets you easily scale the hosting infrastructure. Instead of setting up another physical machine, VM deployment lets you easily create a new isolated environment to run a dedicated workload and application.
Development and Testing Environments
Hypervisor’s isolation allows developers to set up a separate development and testing environment easily. They can do so by creating a virtual machine on the same server or in their local systems.
It enables developers to accurately test new changes to their services or applications without affecting the live server. Moreover, they can determine the ideal resource allocations for the applications before deploying them live.
Setting up a virtual development area is simple since hypervisors let users clone VMs to replicate the live environment. It ensures matching configurations and dependencies between two instances, maintaining the testing accuracy.
The virtual machine’s snapshot and rollback features also help improve development efficiency. Instead of manually reverting the changes, developers can easily restore the system to its previous state when encountering errors.
Disaster Recovery
System administrators commonly implement hypervisors for their disaster recovery and data protection strategy. In addition to the snapshot features, virtual machines are portable and hardware-agnostic, enabling them to adapt to another system without incompatibility issues.
In addition, hypervisors offer a replication capability, allowing the system administrator to mirror the live virtual machines to the backup servers. Some also replicate the data in real time to minimize data loss.
These capabilities allow users to quickly move the virtual machine between hosts if the current system fails, maintaining uptime.
If an accident happens in the live machine, the hypervisor deploys automatic failover to repurpose the secondary system as the new main host.
You can set the backup virtual server in the same machine or a remote system in another geographical location. The latter helps maintain uptime in the event of a natural disaster.
Virtual Desktop Infrastructure (VDI)
A hypervisor allows users to run multiple guest operating systems in a server to create a virtual desktop infrastructure (VDI). It provides users with remote desktop environments, which they can access using a secure protocol.
VDI improves applications and data accessibility since users can manage them anywhere by connecting to the virtual desktop. In addition, you can use any device to access the remote instance.
Regardless of their device’s specifications, users can enjoy the host server’s full hardware capabilities since the workloads run remotely. Moreover, all data resides in a centralized location, minimizing security risks when the endpoint devices are compromised.
Due to these benefits, enterprises use VDI to enable remote working. Instead of provisioning each user with a dedicated device, businesses can save costs and effort by setting up a VDI.
It also simplifies infrastructure management as the system administrator can manage all systems directly from the host machine.
Cloud Computing
Cloud computing providers use a hypervisor to abstract their servers to offer infrastructure as a service (IaaS). This technology enables them to provide on-demand isolated virtual environments for hosting users’ applications.
In cloud environments, users can host all the necessary applications in separate virtual instances within the same server. For example, they can deploy the user-facing service, database, runtime, middleware, and guest operating system.
Hypervisors also make the infrastructure easily scalable. If the user wants to deploy a new application, the cloud provider can quickly provision a new virtual machine in the host system.
Even though the cloud infrastructure is multi-tenant, the hypervisor’s isolation enables users to configure and manage their virtual servers freely. They can also set hardware allocations according to their needs and easily migrate to another infrastructure.
Resource Segmentation
Hypervisors let you divide computing resources like CPU cores, RAM capacity, storage space, and bandwidth in a controlled and isolated manner. In a VPS hosting environment, it ensures each user gets equal allocation.
Resource segmentation is also useful for running different tasks and services on a single server. It guarantees that each process receives enough resources to operate properly.
Controlled resource allocation and isolations also help prevent interferences between applications. Otherwise, it may lead to performance degradation and instability, harming your service’s usability.
Moreover, you can repurpose other processes’ resource allocations for high-priority or urgent tasks. For example, you can prioritize the computing power for an intrusion detection system during a security-critical incident.
Choosing the Right Hypervisor
Selecting the right hypervisor software ensures your IT infrastructure aligns with your needs and performs optimally.
To help you make an informed decision, we have compiled several factors to consider:
- Cost. While some hypervisors are open-source and free, others may cost up to thousands of dollars. When choosing, consider the upfront cost and ongoing expenses for support or maintenance.
- Compatibility. Users must ensure the chosen virtualization software is compatible with their current IT infrastructure, including the hardware, storage solutions, and networking components. Otherwise, it may cause performance or operational issues.
- Licensing. Each hypervisor provider has a different pricing and licensing scheme. For example, some may charge based on the number of sockets, core counts, or VMs.
- Ease-of-use. Several hypervisors offer features that help system administrators easily monitor multiple virtual machines. Choose one with a user-friendly interface, management software, and automation features.
- Security. To ensure optimal IT infrastructure safety, users must choose a hypervisor with robust security features like role-based access control, disk encryption, and secure boot.
- Performance and scalability. Since hypervisors support different numbers of VMs, CPUs, RAM, and storage, choose one that can handle your projected tasks. Also, ensure you can easily add more hosts to scale your IT infrastructure.
When choosing a hypervisor, determine whether you need an on-premise or off-premise one. On-premise refers to self-deployed and managed technology. It means you own and run the computer hardware on which you install the virtualization software.
Meanwhile, service providers will install and manage off-premise hypervisors on their facilities, so users can access the virtualized hardware resources but don’t own the physical server. It is suitable for beginners as they don’t need to manage the entire infrastructure manually.
To build an enterprise infrastructure, we recommend the type 1 bare-metal hypervisor for better performance and isolation. A type 2 hypervisor is more suitable for personal use and local development environments that prioritize simplicity over performance.
If you need off-premise virtualization solutions, ensure the hosting provider supports your hypervisor and offers ample resources. For example, Hostinger KVM VPS hosting plans offer up to 8 vCPU cores, 32 GB of RAM, and 400 GB of NVMe storage.
Hostinger VPS also supports all hypervisors, allowing users to create nested virtualization without incompatibility issues. For example, you can run the open-source Proxmox to create multiple virtual machines on a KVM environment.
We recommend the higher KVM VPS plans to ensure all the guest operating systems receive enough resources. However, you can start with KVM 1, which starts at £5.29/month, and upgrade anytime as needed.
Conclusion
A hypervisor lets users create several virtual machines on top of a single server, each with an isolated resource and operating system. It works by providing an abstraction layer that facilitates data transmission and hardware allocation using methods like API calls.
Depending on the position, there are two types of hypervisors. Type 1 bare-metal hypervisor abstracts the host’s hardware, providing lower latency and higher performance. Meanwhile, type 2 hypervisors sit on top of the main operating system.
This technology helps save costs since you can create many virtual systems on a single machine instead of running multiple servers. Moreover, it provides snapshot and failover features to ensure data safety and server uptime.
Common use cases for hypervisors include enabling server consolidation and creating a development environment. It is also helpful for disaster recovery, deploying virtual desktop infrastructure, creating cloud computing environments, and segmenting server resources.
To choose the right one, consider the hypervisor performance, compatibility, features, and pricing. If you need off-premise virtualization platforms, pick a hosting provider that supports your chosen software and offers ample computing resources, like Hostinger.
What Is a Hypervisor FAQ
In this section, we will answer several common questions about the hypervisor technology.
What Is the Difference Between a Container and a Hypervisor?
A hypervisor provides an abstraction layer on the host’s hardware. Meanwhile, a container abstracts the host operating system.
Containers are lightweight but provide a lower level of isolation and security than a hypervisor. Their common use cases include service deployments, which prioritize speed and efficiency.
What Is a Cloud Hypervisor?
In cloud computing, a hypervisor is a virtualization technology that allows IaaS service providers to abstract their data center to provide virtual servers on demand. It lets users host their applications in an isolated and easily scalable infrastructure.
What Are the Security Concerns for Hypervisors?
Main hypervisor security concerns include improper user access control and unpatched security flaws.
If every user can control all aspects of your hypervisors, they may make unauthorized changes that harm the functionality and data integrity. Meanwhile, using an outdated version exposes all virtual machines to security risks.